Manage and visualize your ACM certificates
This guide demonstrates how to bring your AWS ACM certificate management experience into Port. You will learn how to:
- Ingest ACM certificate data into Port's software catalog using Port's AWS integration.
- Set up self-service actions to manage ACM certificates (request new certificates, renew certificates, and delete certificates).
- Build dashboards in Port to monitor and take action on your ACM resources.
Common use cases
- Monitor the status and expiration of all ACM certificates across accounts from a single view.
- Empower platform teams to automate certificate lifecycle management via GitHub workflows.
- Streamline certificate requests and renewals through self-service actions.
Prerequisites
This guide assumes the following:
-
You have a Port account and have completed the onboarding process.
-
Port's AWS integration is installed in your account.
-
Install the GitHub integration relevant to you:
- GitHub (Legacy)
- GitHub (Ocean)
Port's GitHub app needs to be installed.
Dedicated Workflows RepositoryWe recommend creating a dedicated repository for the workflows that are used by Port actions.
Install GitHub Ocean.
Set up data model
When installing the AWS integration in Port, the AWS Account blueprint is created by default.
However, the ACM Certificate blueprint is not created automatically so we will need to create it manually.
Create the ACM certificate blueprint
-
Go to the Builder page of your portal.
-
Click on
+ Blueprint. -
Click on the
{...}button in the top right corner, and chooseEdit JSON. -
Add this JSON schema:
AWS ACM Certificate blueprint (Click to expand)
{"identifier": "acmCertificate","description": "This blueprint represents an SSL/TLS certificates for your Amazon Web Services-based websites and applications","title": "ACM Certificate","icon": "AWS","schema": {"properties": {"createdAt": {"icon": "DefaultProperty","type": "string","title": "Created At","format": "date-time"},"inUse": {"icon": "DefaultProperty","type": "boolean","title": "In Use"},"keyAlgorithm": {"icon": "DefaultProperty","type": "string","title": "Key Algorithm"},"expirationDate": {"type": "string","title": "Expiration Date","format": "date-time"},"renewalEligibility": {"icon": "DefaultProperty","title": "Renewal Eligibility","type": "string","enum": ["ELIGIBLE","INELIGIBLE"],"enumColors": {"ELIGIBLE": "green","INELIGIBLE": "red"}},"status": {"icon": "DefaultProperty","title": "Status","type": "string","enum": ["ISSUED","EXPIRED","PENDING_VALIDATION","INACTIVE","FAILED","REVOKED","VALIDATION_TIMED_OUT"],"enumColors": {"ISSUED": "green","EXPIRED": "red","PENDING_VALIDATION": "lightGray","INACTIVE": "red","FAILED": "red","REVOKED": "gold","VALIDATION_TIMED_OUT": "gold"}},"type": {"icon": "DefaultProperty","type": "string","title": "Type"},"arn": {"type": "string","title": "Arn"}},"required": []},"mirrorProperties": {},"calculationProperties": {},"aggregationProperties": {},"relations": {"account": {"title": "Account","target": "awsAccount","required": false,"many": false}}} -
Click
Saveto create the blueprint.
Update the integration mapping
-
Go to the Data Sources page of your portal.
-
Select the AWS integration.
-
Add the following YAML block into the editor to ingest ACM certificates from your AWS account:
AWS integration configuration (Click to expand)
deleteDependentEntities: truecreateMissingRelatedEntities: trueenableMergeEntity: trueresources:- kind: AWS::Organizations::Accountselector:query: 'true'port:entity:mappings:identifier: .Idtitle: .Nameblueprint: '"awsAccount"'properties:arn: .Arnemail: .Emailstatus: .Statusjoined_method: .JoinedMethodjoined_timestamp: .JoinedTimestamp | sub(" "; "T")- kind: AWS::ACM::Certificateselector:query: 'true'port:entity:mappings:identifier: .CertificateArntitle: .DomainNameblueprint: '"acmCertificate"'properties:status: .Statustype: .Typearn: .CertificateArnrenewalEligibility: .RenewalEligibilitykeyAlgorithm: .KeyAlgorithminUse: .InUsecreatedAt: .CreatedAtexpirationDate: .NotAfterrelations:account: .__AccountId -
Click
Save & Resyncto apply the mapping.
Set up self-service actions
Now let us create self-service actions to manage your ACM certificates directly from Port using GitHub Actions. You will implement workflows to:
- Request a new ACM certificate.
- Renew an eligible ACM certificate.
- Delete an ACM certificate.
To implement these use-cases, follow the steps below:
Add GitHub secrets
In your GitHub repository, go to Settings > Secrets and add the following secrets:
PORT_CLIENT_ID- Port Client ID learn more.PORT_CLIENT_SECRET- Port Client Secret learn more.AWS_ACCESS_KEY_ID- AWS IAM user's access key.AWS_SECRET_ACCESS_KEY- AWS IAM user's secret access key.AWS_REGION- AWS region (e.g.,us-east-1).
The AWS IAM user must have the following permissions to manage ACM certificates:
acm:RequestCertificateacm:RenewCertificateacm:DeleteCertificate
Request a new ACM certificate
Add GitHub workflow
Create the file .github/workflows/request-acm-cert.yaml in the .github/workflows folder of your repository.
Request ACM Certificate GitHub workflow (Click to expand)
name: Request ACM Certificate
on:
workflow_dispatch:
inputs:
domain_name:
required: true
description: 'The fully qualified domain name (FQDN) that you want to secure with an ACM certificate'
type: string
validation_method:
required: true
description: 'The method you want to use to validate that you own or control domain'
type: string
port_context:
required: true
description: 'Action and general context (blueprint, entity, run id, etc...)'
type: string
jobs:
request-acm:
runs-on: ubuntu-latest
steps:
- name: Inform Port of workflow start
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{fromJson(inputs.port_context).runId}}
logMessage: Configuring AWS credentials to request public ACM cert with domain name ${{ inputs.domain_name }}
- name: Configure AWS credentials
uses: aws-actions/configure-aws-credentials@v4
with:
aws-access-key-id: ${{ secrets.AWS_ACCESS_KEY_ID }}
aws-secret-access-key: ${{ secrets.AWS_SECRET_ACCESS_KEY }}
aws-region: ${{ secrets.AWS_REGION }}
- name: Request ACM certificate
run: aws acm request-certificate --domain-name ${{ inputs.domain_name }} --validation-method ${{ inputs.validation_method }}
- name: Inform Port about ACM certificate success
if: success()
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{ fromJson(inputs.port_context).runId }}
status: 'SUCCESS'
logMessage: ✅ ACM certificate for domain ${{ inputs.domain_name }} requested successfully
summary: ACM certificate requested successfully
- name: Inform Port about ACM certificate failure
if: failure()
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{ fromJson(inputs.port_context).runId }}
status: 'FAILURE'
logMessage: ❌ Failed to request ACM certificate for domain ${{ inputs.domain_name }}
summary: ACM certificate request failed
Create Port action
-
Go to the Self-service page of your portal.
-
Click on the
+ New Actionbutton. -
Click on the
{...} Edit JSONbutton. -
Copy and paste the following JSON configuration into the editor.
- GitHub (Legacy)
- GitHub (Ocean)
Request ACM Certificate action (Click to expand)
Modification RequiredMake sure to replace
<GITHUB_ORG>and<GITHUB_REPO>with your GitHub organization and repository names respectively.{"identifier": "request_acm_certificate","title": "Request ACM Certificate","icon": "AWS","description": "Requests an ACM certificate for use with other Amazon Web Services services","trigger": {"type": "self-service","operation": "CREATE","userInputs": {"properties": {"domain_name": {"icon": "DefaultProperty","type": "string","title": "Domain Name","description": "The fully qualified domain name (FQDN), such as www.example.com, that you want to secure with an ACM certificate"},"validation_method": {"icon": "DefaultProperty","title": "Validation Method","description": "The method you want to use if you are requesting a public certificate to validate that you own or control domain","type": "string","default": "DNS","enum": ["EMAIL","DNS"],"enumColors": {"EMAIL": "lightGray","DNS": "lightGray"}}},"required": ["domain_name","validation_method"],"order": ["domain_name","validation_method"]}},"invocationMethod": {"type": "GITHUB","org": "<GITHUB-ORG>","repo": "<GITHUB-REPO>","workflow": "request-acm-cert.yaml","workflowInputs": {"{{ spreadValue() }}": "{{ .inputs }}","port_context": {"runId": "{{ .run.id }}"}},"reportWorkflowStatus": true},"requiredApproval": false}Request ACM Certificate action (Click to expand)
Replace the variables<GITHUB-ORG>- your GitHub organization or user name.<GITHUB-REPO>- your GitHub repository name.<YOUR_GITHUB_OCEAN_INTEGRATION_ID>- your GitHub Ocean integration installation ID.
{"identifier": "request_acm_certificate","title": "Request ACM Certificate","icon": "AWS","description": "Requests an ACM certificate for use with other Amazon Web Services services","trigger": {"type": "self-service","operation": "CREATE","userInputs": {"properties": {"domain_name": {"icon": "DefaultProperty","type": "string","title": "Domain Name","description": "The fully qualified domain name (FQDN), such as www.example.com, that you want to secure with an ACM certificate"},"validation_method": {"icon": "DefaultProperty","title": "Validation Method","description": "The method you want to use if you are requesting a public certificate to validate that you own or control domain","type": "string","default": "DNS","enum": ["EMAIL","DNS"],"enumColors": {"EMAIL": "lightGray","DNS": "lightGray"}}},"required": ["domain_name","validation_method"],"order": ["domain_name","validation_method"]}},"invocationMethod": {"type": "INTEGRATION_ACTION","installationId": "<YOUR_GITHUB_OCEAN_INTEGRATION_ID>","integrationActionType": "dispatch_workflow","integrationActionExecutionProperties": {"org": "<GITHUB-ORG>","repo": "<GITHUB-REPO>","workflow": "request-acm-cert.yaml","workflowInputs": {"{{ spreadValue() }}": "{{ .inputs }}","port_context": {"runId": "{{ .run.id }}"}},"reportWorkflowStatus": true}},"requiredApproval": false} -
Click
Save.
Now you should see the Request ACM Certificate action in the self-service page. 🎉
Renew an ACM certificate
Add GitHub workflow
Create the file .github/workflows/renew-acm-cert.yaml in the .github/workflows folder of your repository.
Renew ACM Certificate GitHub workflow (Click to expand)
name: Renew ACM Certificate
on:
workflow_dispatch:
inputs:
port_context:
required: true
description: 'Action and general context (blueprint, entity, run id, etc...)'
type: string
jobs:
renew-acm-cert:
runs-on: ubuntu-latest
steps:
- name: Inform Port of workflow start
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{fromJson(inputs.port_context).runId}}
logMessage: Configuring AWS credentials to Renew ACM certificate with domain ${{ fromJson(inputs.port_context).entity.title }}
- name: Configure AWS credentials
uses: aws-actions/configure-aws-credentials@v4
with:
aws-access-key-id: ${{ secrets.AWS_ACCESS_KEY_ID }}
aws-secret-access-key: ${{ secrets.AWS_SECRET_ACCESS_KEY }}
aws-region: ${{ secrets.AWS_REGION }}
- name: Renew ACM certificate
run: aws acm renew-certificate --certificate-arn ${{ fromJson(inputs.port_context).entity.properties.arn }}
- name: Inform Port about ACM certificate renewal success
if: success()
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{ fromJson(inputs.port_context).runId }}
status: 'SUCCESS'
logMessage: ✅ ACM certificate with domain name ${{ fromJson(inputs.port_context).entity.title }} renewed successfully
summary: ACM certificate renewal completed successfully
- name: Inform Port about ACM certificate renewal failure
if: failure()
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{ fromJson(inputs.port_context).runId }}
status: 'FAILURE'
logMessage: ❌ Failed to Renew ACM certificate with domain name ${{ fromJson(inputs.port_context).entity.title }}
summary: ACM certificate renewal failed
Create Port action
-
Go to the Self-service page of your portal.
-
Click on the
+ New Actionbutton. -
Click on the
{...} Edit JSONbutton. -
Copy and paste the following JSON configuration into the editor.
- GitHub (Legacy)
- GitHub (Ocean)
Renew ACM Certificate action (Click to expand)
Modification RequiredMake sure to replace
<GITHUB_ORG>and<GITHUB_REPO>with your GitHub organization and repository names respectively.{"identifier": "renew_acm_certificate","title": "Renew ACM Certificate","icon": "AWS","description": "Renews an eligible ACM certificate","trigger": {"type": "self-service","operation": "DAY-2","userInputs": {"properties": {},"required": [],"order": []},"condition": {"type": "SEARCH","rules": [{"property": "renewalEligibility","operator": "=","value": "ELIGIBLE"}],"combinator": "and"},"blueprintIdentifier": "acmCertificate"},"invocationMethod": {"type": "GITHUB","org": "<GITHUB-ORG>","repo": "<GITHUB-REPO>","workflow": "renew-acm-cert.yaml","workflowInputs": {"port_context": {"runId": "{{ .run.id }}","entity": "{{ .entity }}"}},"reportWorkflowStatus": true},"requiredApproval": false}Renew ACM Certificate action (Click to expand)
Replace the variables<GITHUB-ORG>- your GitHub organization or user name.<GITHUB-REPO>- your GitHub repository name.<YOUR_GITHUB_OCEAN_INTEGRATION_ID>- your GitHub Ocean integration installation ID.
{"identifier": "renew_acm_certificate","title": "Renew ACM Certificate","icon": "AWS","description": "Renews an eligible ACM certificate","trigger": {"type": "self-service","operation": "DAY-2","userInputs": {"properties": {},"required": [],"order": []},"condition": {"type": "SEARCH","rules": [{"property": "renewalEligibility","operator": "=","value": "ELIGIBLE"}],"combinator": "and"},"blueprintIdentifier": "acmCertificate"},"invocationMethod": {"type": "INTEGRATION_ACTION","installationId": "<YOUR_GITHUB_OCEAN_INTEGRATION_ID>","integrationActionType": "dispatch_workflow","integrationActionExecutionProperties": {"org": "<GITHUB-ORG>","repo": "<GITHUB-REPO>","workflow": "renew-acm-cert.yaml","workflowInputs": {"port_context": {"runId": "{{ .run.id }}","entity": "{{ .entity }}"}},"reportWorkflowStatus": true}},"requiredApproval": false} -
Click
Save.
Now you should see the Renew ACM Certificate action in the self-service page. 🎉
The renew action will only be visible for certificates that have renewalEligibility set to ELIGIBLE. This ensures users can only renew certificates that are actually eligible for renewal.
Delete an ACM certificate
Add GitHub workflow
Create the file .github/workflows/delete-acm-cert.yaml in the .github/workflows folder of your repository.
Delete ACM Certificate GitHub workflow (Click to expand)
name: Delete ACM Certificate
on:
workflow_dispatch:
inputs:
port_context:
required: true
description: 'Action and general context (blueprint, entity, run id, etc...)'
type: string
jobs:
delete-acm-cert:
runs-on: ubuntu-latest
steps:
- name: Inform Port of workflow start
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{fromJson(inputs.port_context).runId}}
logMessage: Configuring AWS credentials to delete ACM certificate with domain ${{ fromJson(inputs.port_context).entity.title }}
- name: Configure AWS credentials
uses: aws-actions/configure-aws-credentials@v4
with:
aws-access-key-id: ${{ secrets.AWS_ACCESS_KEY_ID }}
aws-secret-access-key: ${{ secrets.AWS_SECRET_ACCESS_KEY }}
aws-region: ${{ secrets.AWS_REGION }}
- name: Delete ACM certificate
run: aws acm delete-certificate --certificate-arn ${{ fromJson(inputs.port_context).entity.properties.arn }}
- name: Inform Port about ACM certificate deletion success
if: success()
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{ fromJson(inputs.port_context).runId }}
status: 'SUCCESS'
logMessage: ✅ ACM certificate with domain name ${{ fromJson(inputs.port_context).entity.title }} deleted successfully
summary: ACM certificate deletion completed successfully
- name: Inform Port about ACM certificate deletion failure
if: failure()
uses: port-labs/port-github-action@v1
with:
clientId: ${{ secrets.PORT_CLIENT_ID }}
clientSecret: ${{ secrets.PORT_CLIENT_SECRET }}
baseUrl: https://api.port.io
operation: PATCH_RUN
runId: ${{ fromJson(inputs.port_context).runId }}
status: 'FAILURE'
logMessage: ❌ Failed to delete ACM certificate with domain name ${{ fromJson(inputs.port_context).entity.title }}
summary: ACM certificate deletion failed
Create Port action
-
Go to the Self-service page of your portal.
-
Click on the
+ New Actionbutton. -
Click on the
{...} Edit JSONbutton. -
Copy and paste the following JSON configuration into the editor.
- GitHub (Legacy)
- GitHub (Ocean)
Delete ACM Certificate action (Click to expand)
Modification RequiredMake sure to replace
<GITHUB_ORG>and<GITHUB_REPO>with your GitHub organization and repository names respectively.{"identifier": "delete_acm_certification","title": "Delete ACM Certification","icon": "AWS","description": "Deletes a certificate and its associated private key.","trigger": {"type": "self-service","operation": "DELETE","userInputs": {"properties": {},"required": [],"order": []},"blueprintIdentifier": "acmCertificate"},"invocationMethod": {"type": "GITHUB","org": "<GITHUB-ORG>","repo": "<GITHUB-REPO>","workflow": "delete-acm-cert.yaml","workflowInputs": {"port_context": {"runId": "{{ .run.id }}","entity": "{{ .entity }}"}},"reportWorkflowStatus": true},"requiredApproval": false}Delete ACM Certificate action (Click to expand)
Replace the variables<GITHUB-ORG>- your GitHub organization or user name.<GITHUB-REPO>- your GitHub repository name.<YOUR_GITHUB_OCEAN_INTEGRATION_ID>- your GitHub Ocean integration installation ID.
{"identifier": "delete_acm_certification","title": "Delete ACM Certification","icon": "AWS","description": "Deletes a certificate and its associated private key.","trigger": {"type": "self-service","operation": "DELETE","userInputs": {"properties": {},"required": [],"order": []},"blueprintIdentifier": "acmCertificate"},"invocationMethod": {"type": "INTEGRATION_ACTION","installationId": "<YOUR_GITHUB_OCEAN_INTEGRATION_ID>","integrationActionType": "dispatch_workflow","integrationActionExecutionProperties": {"org": "<GITHUB-ORG>","repo": "<GITHUB-REPO>","workflow": "delete-acm-cert.yaml","workflowInputs": {"port_context": {"runId": "{{ .run.id }}","entity": "{{ .entity }}"}},"reportWorkflowStatus": true}},"requiredApproval": false} -
Click
Save.
Now you should see the Delete ACM Certification action in the self-service page. 🎉
The delete action permanently removes the certificate and its associated private key. This operation cannot be undone, so use it carefully.
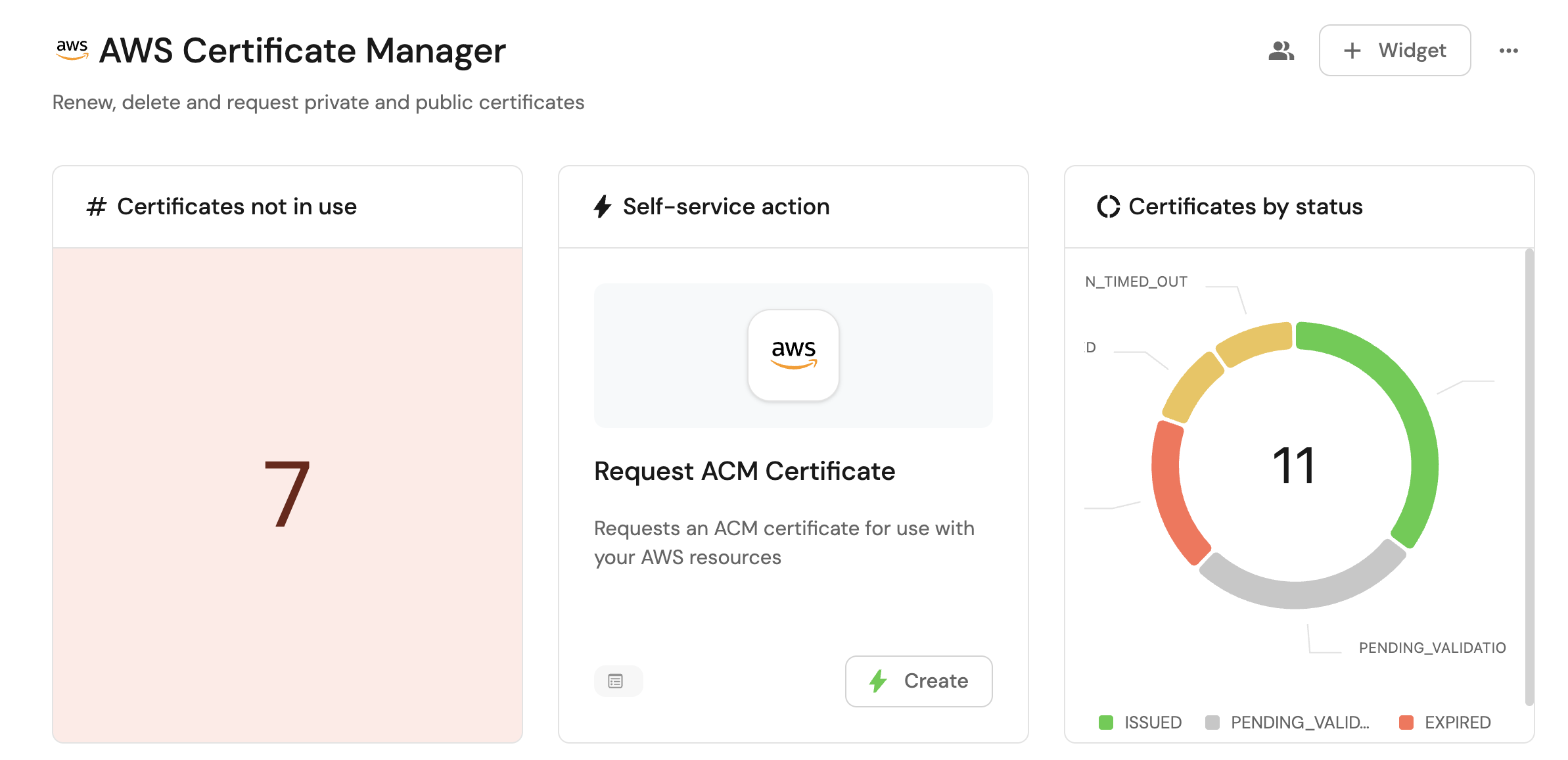
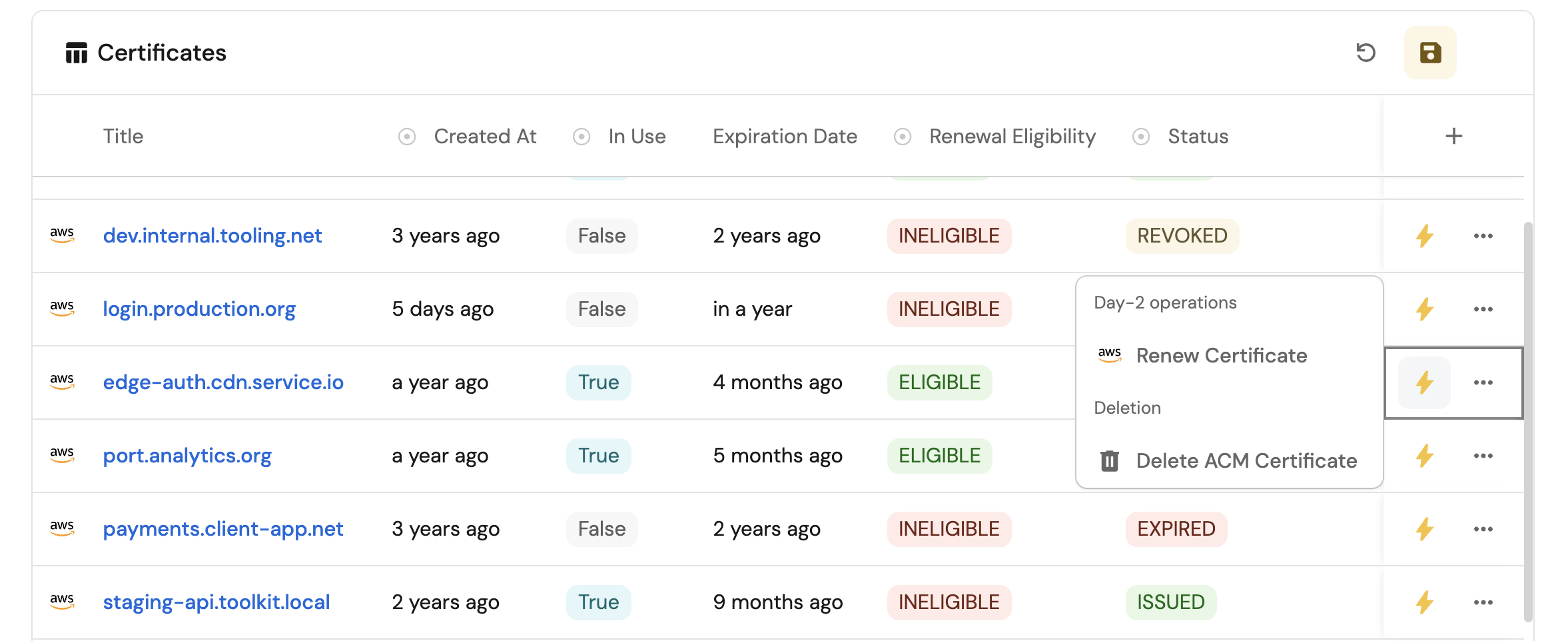
Visualize certificate metrics
With your data and actions in place, we can create a dedicated dashboard in Port to visualize all ACM certificates by status, usage, and expiration. In addition, we can trigger actions (request new certificate, renew, delete) directly from the dashboard.
Create a dashboard
- Go to your software catalog.
- Click on the
+button in the left sidebar. - Select New dashboard.
- Name the dashboard ACM Certificate Management.
- Input
Monitor and manage your AWS ACM certificatesunder Description. - Select the
AWSicon. - Click
Create.
We now have a blank dashboard where we can start adding widgets to visualize insights from our AWS ACM certificates.
Add widgets
In the new dashboard, create the following widgets:
Certificates not in use (click to expand)
- Click
+ Widgetand select Number Chart. - Title:
Certificates not in use(add theAWSicon). - Select
Count entitiesChart type and choose ACM Certificate as the Blueprint. - Select
countfor the Function. - Add this JSON to the Additional filters editor to filter certificates not in use:
[{"combinator":"and","rules":[{"property":"inUse","operator":"=","value": false}]}]
- Select
customas the Unit and inputcertificatesas the Custom unit. - Click Save.
Certificates by status (click to expand)
- Click
+ Widgetand select Pie chart. - Title:
Certificates by status(add theAWSicon). - Choose the ACM Certificate blueprint.
- Under
Breakdown by property, select the Status property. - Click Save.
Expired certificates table (click to expand)
- Click
+ Widgetand select Table. - Title:
Expired certificates(add theAWSicon). - Choose the ACM Certificate blueprint.
- Add this JSON to the Additional filters editor to filter expired certificates:
{"combinator":"and","rules":[{"operator":"=","value":"acmCertificate","property":"$blueprint"},{"operator":"=","value":"EXPIRED","property":"status"}]}
- Click Save to add the widget to the dashboard.
- Click on the
...button in the top right corner of the table and select Customize table. - In the top right corner of the table, click on
Manage Propertiesand add the following properties:- Title: The certificate domain name.
- Status: The current status of the certificate.
- Expiration Date: When the certificate expired.
- Account: The name of each related AWS account.
- In Use: Whether the certificate is currently in use.
- Click on the save icon in the top right corner of the widget to save the customized table.
Request new certificate action (click to expand)
- Click
+ Widgetand select Action card. - Choose the Request ACM Certificate action we created in this guide.
- Click Save.